Blockchain technology, known for its decentralized and immutable nature, presents a revolutionary approach to data storage and verification. However, this same immutability clashes with increasingly more stringent data protection laws, particularly with the European Union’s (E.U.) General Data Protection Regulation (GDPR). At the core of this conflict is the “right to be forgotten,” a principle allowing individuals to request the deletion of their personal data. Blockchain’s design, which ensures that once data is added to the digital ledger, it cannot be changed or deleted, directly contradicts GDPR’s mandates.
This article explores the inherent tension between blockchain’s immutability and the GDPR’s data protection requirements, focusing on the technical and legal challenges blockchain faces in complying with these regulations.
Blockchain’s Beginnings
In 1991, cryptography researchers, Stuart Haber, PhD, and W. Scott Stornetta, PhD, proposed blockchain technology to securely timestamp digital documents and protect them from tampering.[i] Nearly 20 years later, an individual or group under the pseudonym “Satoshi Nakamoto” introduced a practical application of blockchain in a white paper, using it as the underlying technology for Bitcoin, a decentralized digital currency.[ii] Their goal was to create a decentralized digital currency system that would eliminate the need for traditional intermediaries, such as banks, allowing users to transact directly with one another in a secure and transparent manner. Central to this idea was the blockchain ledger: a distributed, immutable record of transactions validated through consensus across multiple nodes on a network. This design was intended to ensure data integrity, prevent double-spending (the risk of digital currency being spent more than once) and provide transparency without relying on centralized authorities.
Nakamoto’s breakthrough addressed specific issues within digital transactions, particularly the need for a trustless system where participants could securely exchange value without relying on a central entity. In recent years, blockchain technology has gained traction and application beyond cryptocurrency, driven by an interest in its potential for enhancing data security, transparency and efficiency across various sectors. From supply chain management to finance, healthcare and voting systems, blockchain is increasingly implemented for its ability to create tamper-resistant, decentralized systems that can streamline processes, reduce fraud and ensure data integrity.
Blockchain’s Immutability & Importance
Blockchain is a decentralized digital ledger system that records transactions across a network of computers.[iii] Unlike traditional databases, which are controlled by a single entity, blockchain’s key feature is decentralization, by which control is distributed among all participants in the network. Every participant, or node, maintains a complete copy of the blockchain, and each node independently verifies and updates the ledger.[iv] This structure ensures that the information stored on the blockchain is transparent and resistant to manipulation.
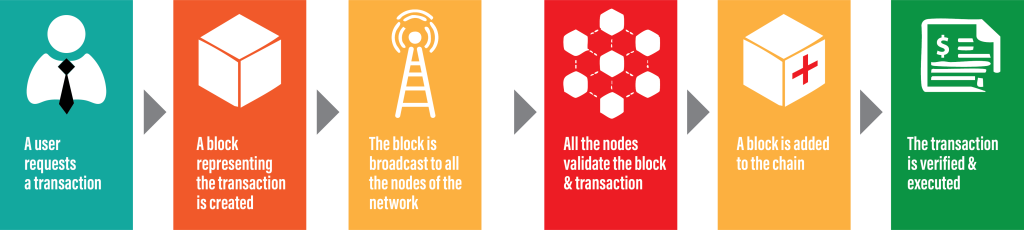
A blockchain operates by grouping transactions into blocks.[v] These blocks are linked together in chronological order to form a continuous chain. Each block contains three primary elements: (1) data, which consists of information about the transactions; (2) a hash, which is a unique identifier for the block, generated using cryptographic algorithms; and (3) the preceding block’s hash, which links the blocks together.
When a transaction is initiated, it is broadcast to the network. Multiple nodes verify the transaction through a consensus mechanism, such as Proof of Work (PoW) or Proof of Stake (PoS). Once verified, the transaction is added to a new block. Each block is cryptographically linked to the previous one via its hash, creating an immutable chain of records.
One of blockchain’s defining features is its immutability, meaning that once data is recorded on the blockchain, it cannot be altered or deleted without extraordinarily difficulty.[vi]This immutability is a direct result of blockchain’s cryptographic hashing and decentralization.
Each block in the blockchain is assigned a unique hash based on its contents. A hash is a long string of letters and numbers created by a cryptographic algorithm.[vii] It functions like a digital fingerprint: If the contents of a block are changed even slightly, the hash changes entirely. Since each block contains the hash of the previous block, any alteration to one block will cascade through the entire blockchain, disrupting the links between all subsequent blocks. For example, if someone attempted to alter a transaction recorded in Block 5 of a 10-block chain, he or she would not only need to change the hash of Block 5, but he or she would also need to change the hashes of Blocks 6 through 10 to maintain the chain. This process would require an enormous amount of computational power, making it practically impossible to alter blockchain data once it has been verified and added.
Blockchain’s decentralized structure further enhances its immutability. Since no single entity controls the entire network, altering the data requires widespread consensus among the network’s participants. For example, under PoW, changing a block would require redoing the complex calculations (called “mining”) for not just the altered block, but all blocks following it.[viii] Moreover, because blockchain networks typically span thousands of nodes, a single bad actor would need to control more than half of the network’s computational power to successfully alter the ledger. This is highly improbable in a large, distributed network. In PoS systems, immutability is enforced differently but with the same goal in mind: Any attempts to alter the blockchain require controlling a significant portion of the network’s resources, which becomes increasingly expensive and difficult as the network grows.
Immutability is a fundamental attribute of blockchain, underpinning its security and trustworthiness. Because records are permanent and cannot be altered without invalidating the entire chain, participants can trust that the data on the blockchain is accurate and tamper-proof. This property makes blockchain particularly valuable in industries such as finance, supply chain management and legal records, where the integrity of data is paramount. For example, in a financial transaction recorded on a blockchain, immutability ensures that once a payment has been made, it cannot be undone or falsified without leaving a trace. Similarly, in a supply chain application, immutability guarantees that the origin and movement of goods can be traced without fear of alteration, creating transparency and accountability.
In summary, blockchain’s immutability is a critical component of its design, driven by its decentralized nature and reliance on cryptographic hashing. This immutability ensures that once data is recorded on the blockchain, it is permanent, secure and resistant to manipulation—an attribute that both enhances trust in the system and presents challenges when considering how blockchain intersects with data-protection laws such as GDPR.
GDPR & the Right to be Forgotten
GDPR is a comprehensive data protection law enacted by the E.U. in 2018.[ix] It governs how organizations collect, process and store the personal data of individuals in the E.U. and in the European Economic Area, which includes the E.U. countries and Norway, Iceland and Liechtenstein. GDPR applies when “the use of personal data by a business relates to the offering of goods or services to individuals in the E.U., irrespective of whether a payment is required, or [involves] monitoring of those in the E.U.”[x]
GDPR imposes strict requirements and significant penalties for noncompliance.[xi] The regulation’s primary aim is to give individuals greater control over their personal information and to ensure that data is handled responsibly by organizations.
One of the GDPR’s most significant provisions is the right to be forgotten, also referred to as the right of erasure, which is codified in Article 17. GDPR defines personal information as:
any information that is relating to an identified or identifiable natural person; an identifiable natural person is one who can be identified, directly or indirectly, in particular by reference to an identifier such as a name, an identification number, location data, an online identifier or to one or more factors specific to the physical, physiological, genetic, mental, economic, cultural or social identity of that natural person.[xii]
GDPR’s Article 17 empowers individuals to have their data removed from an organization’s records when the retention of that data is no longer justified. The key situations in which the right to be forgotten applies include when data is no longer necessary, when there is a withdrawal of consent, an objection to processing, unlawful processing, a legal obligation and special provisions regarding data belonging to minors and children.
The right to be forgotten places an obligation on organizations to respond to requests for data deletion without undue delay. However, there are certain exceptions to this right. For example, controllers are not required to delete data if it is necessary “for exercising the right of freedom of expression and information,” necessary for complying with legal obligations, or for the establishment, exercise or defense of legal claims. The right to be forgotten is significant because it addresses growing concerns about data permanence in the digital age. In today’s interconnected world, personal information is often widely disseminated across the internet and various platforms. Data can live on indefinitely, which poses privacy risks, especially in cases where the data is misused or the individual no longer wishes for it to be available. Article 17 provides individuals with a way to regain control over their personal information by allowing them to request the erasure of data that no longer serves a legitimate purpose. This right is particularly important where outdated, inaccurate or harmful information remains accessible online or within databases, potentially impacting an individual’s reputation or privacy.
Conflict Between Article 17 & Blockchain’s Immutability
One of the most interesting conflicts arises when the right to be forgotten is applied to emerging technologies such as blockchain, which by design is immutable. This presents a fundamental clash between GDPR’s emphasis on giving individuals the right to erase personal data and blockchain’s core feature of ensuring that all records are permanent and tamper-proof. Reconciling these two opposing concepts is one of the key legal challenges facing blockchain technology integration today.
If personal data is stored on a public or private blockchain, there is no straightforward mechanism to remove or delete that data once it has been committed to the chain.[xiii] Unlike traditional centralized systems, where a database administrator can simply delete an entry, blockchain’s decentralized and cryptographic structure is not designed to support deletion or modification of data. Once the data is inscribed to the blockchain, it becomes part of the permanent record, potentially visible to all participants in the network. This structure poses significant challenges for organizations seeking to comply with GDPR, as it is unclear how they could honor requests to delete data without undermining the security and integrity of the blockchain.[xiv]
The conflict is most acute in public blockchains, which are fully decentralized and involve thousands of independent participants who share and validate data. In a public blockchain, once personal data is recorded, it is replicated across the entire network, making it impossible to remove without disrupting the consensus mechanism maintaining the blockchain’s integrity. Even if a single participant was willing to comply with a right to erasure request, he or she lacks the technical ability to erase data across the entire network. While private or permissioned blockchains offer slightly more flexibility in this regard, they still face challenges in fully complying with GDPR. In a permissioned blockchain, a select group of participants controls the validation and governance of the ledger, which theoretically provides a mechanism for deleting or masking data. However, even in these cases, the decentralized structure of blockchain means that data is distributed among multiple participants, and fully erasing that data may not be technically feasible.
Another layer of complexity in reconciling GDPR with blockchain’s immutability is determining what constitutes personal data on the blockchain. Blockchain often uses pseudonymized or encrypted data, where users interact with the system through cryptographic keys rather than real-world identifiers like names or addresses. While pseudonymization offers some degree of privacy protection, the GDPR defines personal data broadly, including any information that can be linked back to an identifiable individual. This means that even though blockchain transactions may not contain explicit personal information, data linked to a cryptographic key could still be considered personal data under the GDPR, if the key can be associated with a specific individual through external information.
Potential Technical Solutions to Compliance
Despite the fundamental conflict between blockchain’s immutability and GDPR’s right to be forgotten, several potential technical solutions have been proposed to bring blockchain systems closer to GDPR compliance. These solutions aim to address the tension between the need for permanent records in a blockchain and GDPR’s requirement to allow individuals to delete their personal data when necessary. While these strategies offer some potential for mitigating the conflict, none fully resolves the underlying issues, and they often come with their own limitations.
Off-Chain Storage
One of the most promising approaches to reconciling blockchain immutability with GDPR compliance is the use of off-chain storage. In this model, personal data is stored outside the blockchain, and only a reference to the data, such as a cryptographic hash or pointer, is recorded on the blockchain. This reference can validate the existence and integrity of the off-chain data without exposing the personal data itself to the blockchain’s immutable ledger.
When a right to erasure request is made under GDPR, the organization can delete the personal data from the off-chain storage while leaving the reference on the blockchain intact. Since the reference is no longer tied to any data, it is rendered meaningless, and the blockchain’s integrity remains preserved. However, while the hash may become meaningless, it still exists on-chain, and depending on the interpretation of GDPR, this could be considered a violation. There is also a theoretical risk of reverse-engineering the hash or combining it with external data to re-identify individuals. While unlikely, this remains a potential concern.
While off-chain storage provides a mechanism for data erasure, it introduces several concerns. The integrity and security of the off-chain data must be robust to prevent unauthorized access or modification. Additionally, organizations must manage this data using centralized servers, which can undermine the decentralized nature of blockchain. However, hybrid models or decentralized file storage solutions offer alternatives that aim to maintain decentralization while storing data off-chain. Still, this reliance on external, centralized or semi-centralized databases reintroduces traditional data management risks, such as reduced transparency and trust. Ultimately, off-chain storage compromises one of blockchain’s core strengths—its trustless, decentralized operation—while adding potential vulnerabilities in securing the off-chain data.
Encryption Key Destruction
Another proposed solution involves the use of encryption to protect personal data on the blockchain, combined with a process known as key destruction. In this model, personal data is encrypted before it is recorded on the blockchain. The data can only be accessed or read by those who possess the encryption key. If an individual requests the deletion of his or her personal data under GDPR, the organization can delete or render the encryption key unusable, effectively making the data on the blockchain inaccessible. While the data remains on the blockchain, destroying the encryption key ensures the information cannot be decrypted, thus satisfying GDPR’s requirement to prevent further processing or use of the personal data.
This method provides a practical workaround preserving the immutability of the blockchain, while still allowing for the functional equivalent of deletion. Furthermore, since GDPR aims to protect the personal data of identifiable people, if the data cannot be matched with a specific person, there would be no data breach. Accordingly, GDPR “does not apply to anonymous information, namely information which does not relate to an identified or identifiable natural person or to personal data rendered anonymous in such a manner that the data subject is not or no longer identifiable.”[xv]
However, this solution is not without limitations. Although encrypted data may become inaccessible, it still technically remains on the blockchain, which may not fully satisfy GDPR’s requirement to erase personal data. There is also the risk that advancements in computing, such as quantum computing, could eventually break the encryption without needing the key. While encryption and key destruction offer a promising strategy, it does not completely eliminate the risk that the data could resurface in the future.
Permissioned Blockchains
Private or permissioned blockchains offer another avenue for attempting GDPR compliance. Unlike public blockchains, where anyone can participate in maintaining and verifying the ledger, permissioned blockchains are managed by a smaller group of trusted entities.[xvi] These entities have greater control over who can join the network and what data can be stored, providing more flexibility in handling sensitive information.
In a permissioned blockchain, governance rules can be implemented allowing for the deletion or masking of personal data upon request. This could involve creating a governance structure in which specific nodes or participants are authorized to carry out deletion requests in response to GDPR erasure claims. Additionally, this use of selective transparency—where personal data is hidden from most participants while still being validated by a few authorized nodes—can help maintain compliance while preserving some degree of blockchain immutability.
Despite this flexibility, even permissioned blockchains face challenges when it comes to true compliance with GDPR’s Article 17. While records may be concealed or “soft deleted,” they often remain on the blockchain and could potentially be recovered by those with sufficient technical expertise. This means that, much like encryption and off-chain storage, permissioned blockchains provide a workaround but do not fully align with GDPR’s erasure requirements.
Additionally, permissioned blockchains often reintroduce elements of centralization, which can undermine some of the benefits of decentralized systems, such as security, transparency and trust. “While permissioned blockchains have many benefits, it is important to note that they lack one of the main pros of public blockchains: a decentralized system.”[xvii] Centralized authorities have more control over data and can therefore alter it without fear of oversight.
There is also debate about the strengths and weaknesses of exempting permissioned blockchains from GDPR regulation. Arguments against exempting permissioned blockchains emphasize that they are fundamentally similar to traditional company databases, offering no significant advantages justifying such an exemption. Hashed personal data is still likely considered pseudonymized data, exposing individuals to risks concerning their data privacy, which supports denying an exemption.
Arguments in support of an exemption highlight that a more flexible interpretation of the regulation could allow for the use of permissioned blockchains without violating personal data protections. Proponents argue that if hashed data can be considered anonymized rather than pseudonymized, then the unique traceability risks associated with permissioned blockchains are minimal and would still align with GDPR’s goals of transparency and accountability. Further, they contend that stifling blockchain innovation through stringent regulations risks hindering technological growth. This argument urges regulators to adapt the GDPR framework to support and encourage technological advancements and privacy layers to evolve along with data protection policies.
Guidance from the E.U.
Recognizing the discrepancies between implementing blockchain technology and ensuring GDPR compliance, the E.U. has formed a working group to closely study and scrutinize these competing causes.[xviii] Multiple rounds of studies and analysis have been conducted, but the theme of uncertainty remains the same. However, the European Parliament’s Science and Technology Options Assessment (STOA) panel has compiled three key policy options to best support GDPR compliance in blockchain applications, emphasizing the need for legal clarity and practical application: the need for regulatory guidance, codes of conduct and certification mechanisms, and funding further research.
There is currently a significant lack of legal certainty in applying GDPR principles to blockchain. To address this, the E.U. suggests specific regulatory guidance on how GDPR should be interpreted in the blockchain context. This could involve coordinated efforts by supervisory authorities and the European Data Protection Board, as well as updates to Article 29 Working Party opinions on topics such as anonymization. Regulatory guidance could help clarify compliance requirements for blockchain developers.
Since GDPR is designed to be technology-neutral, it allows for the creation of sector-specific codes of conduct and certification mechanisms to help interpret data protection requirements in specialized areas. These mechanisms, which encourage a collaborative approach between regulators and the private sector, have proven effective in other areas, such as cloud computing. Similar initiatives tailored to blockchain could provide actionable frameworks for GDPR compliance.
While regulatory guidance and certification mechanisms are helpful, they may not fully resolve technical challenges, such as blockchain’s inherent resistance to data erasure. Therefore, E.U. research funding could foster interdisciplinary studies to develop blockchain protocols and governance models designed for GDPR compliance, addressing both technical and organizational hurdles in managing distributed data controllers and enabling data deletion.
While studies like these are great first steps in initiating discussions on blockchain’s GDPR compliance, their impact is limited, as they lack the authority of official regulations or laws. Without formal legislative action, the guidance they provide remains advisory rather than enforceable.
The conflict between blockchain’s immutability and the GDPR’s right to be forgotten presents a complex challenge for data privacy in an era of emerging technologies. While blockchain’s decentralized, tamper-proof nature is a key feature for security and trust, it inherently clashes with GDPR’s mandate for erasing personal data, particularly under Article 17. Potential technical solutions, such as off-chain storage, encryption with key destruction and permissioned blockchains, offer pathways toward compliance, but each comes with limitations. Ultimately, achieving a balance between privacy rights and the integrity of blockchain systems will require further legal and technological innovation.
REFERENCES
[i] Shashank, “History of blockchain technology,” Blockverse, (last updated August 22, 2024) https://www.theblockverse.co/history-of-blockchain/.
[ii] Satoshi Nakamoto, “Bitcoin: A Peer-to-Peer Electronic Cash System” (2009) (available at https://bitcoin.org/en/bitcoin-paper) (explaining that the decentralized peer-to-peer structure of blockchain technology prevents double-spend concerns).
[iii] Blockchain, Merriam-Webster’s Dictionary, https://www.merriam-webster.com/dictionary/blockchain (last visited Oct. 25, 2024) (defining blockchain as “a digital database containing information that can be simultaneously used and shared within a large decentralized, publicly accessible network.”).
[iv] Jaliz Maldonado, “10 Ways Blockchain Technology Will Change the Legal Industry,” XIV National Law Review 246 (2018).
[v] Anisha Mirchandani, “Note: The GDPR-Blockchain Paradox: Exempting Permissioned Blockchains from the GDPR,” 29 Fordham Intell. Prop. Media & Ent. L.J. 1201 (2019).
[vi] J. Collin Spring, “The Blockchain Paradox: Almost Always Reliable, Almost Never Admissible,” 72 SMU L. Rev. 925 (2019).
[vii] Jessica Peel, “The GDPR: The Biggest Threat to the Implementation of Blockchain Technology in Global Supply Chains,” 88 UMKC L. Rev. 497, 507, 509 (2019).
[viii] Simon Chandler, “Proof of stake vs. proof of work: key differences between these methods of verifying cryptocurrency transactions, Business Insider” (last visited Oct. 10, 2024, 9:04 A.M.), https://www.businessinsider.com/personal-finance/investing/proof-of-stake-vs-proof-of-work.
[ix] Jeff Kosseff, Cybersecurity Law 410 (3rd ed. 2022).
[x] See European Data Protection Law and Practice 50 (Eduardo Ustaran ed., 2018).
[xi] GDPR art. 83(4)-(5). Severe violations may incur fines up to 20 million euros, with less severe violations up to 10 million euros.
[xii] GDPR art. 4(1).
[xiii] Bisma Shoaib, “The Immutable Blockchain Confronts the Unstoppable GDPR,” 14 Seattle J. of Env’t L. 1, 3 (2023).
[xiv] Id. at 10, 15, 16-21.
[xv] “European Data Protection Law and Practice,” supra note 21, at 71.
[xvi] Shoaib, supra note 29, at 18-20.
[xvii] Mirchandani, supra note 9, at 1215, 1223-33.
[xviii] Dr. Michèle Finck, “Study—Blockchain and the General Data Protection Regulation—Can distributed ledgers be squared with European data protection law?”, European Parliament Panel for the Future of Science and Technology, 96-99 (2019). The GDPR is designed to be technology-neutral, ensuring that personal data is protected no matter the technology or storage method used. Whether an entity manages personal data through advanced systems or paper records, it remains subject to GDPR requirements.
Bridget Grathwohl, Juris Doctor candidate, School of Law, University of North Dakota
Bridget Grathwohl is a third-year Juris Doctor candidate at the UND’s School of Law. Grathwohl attended Minnesota State University Moorhead and earned degrees in Political Science and Communication Studies. She has authored and co-authored several publications, including an article for the North Dakota Law Review. Grathwohl has been a member of the North Dakota Law Review since 2023 and serves as the journal’s Student Articles Editor. Grathwohl expects to earn her JD in the spring of 2025. After graduation, she is set to clerk for a federal judge in the District of North Dakota.